
Hackers Target Government Defense Contractors with New Backdoor Malware.

Hackers Target Government Defense Contractors with New Backdoor Malware
Microsoft has recently revealed that APT33, an Iranian cyber-espionage group also known as Peach Sandstorm, HOLMIUM, or Refined Kitten, is targeting defense contractors around the globe with a newly discovered backdoor malware called FalseFront. This targeted attack underscores the persistent threat these state-backed hackers pose to the security of sensitive technologies and information.

What is the New "FalseFront" Backdoor Malware Attack?
FalseFront is a custom-built backdoor malware that grants APT33 operatives remote access to compromised systems, allowing them to execute programs and steal data within infected networks. Once stolen, it enables file transfer to its command-and-control (C2) servers.
FalseFront marks a worrying evolution in APT33’s capabilities. Its first observation in the wild dates back to early November 2023, indicating a relatively recent development. Microsoft also highlights that its design aligns with past APT33 tactics, suggesting a continual refinement of their cyber-espionage toolset.

Defense Industrial Base (DIB) Targeted by Iranian Sponsored APT33
The APT33 attacks specifically target the Defense Industrial Base (DIB), a network of over 100,000 defense companies and subcontractors responsible for researching and developing military weapons systems, subsystems, and components. This isn’t the first time APT33 has set its sights on the DIB.
In September 2023, Microsoft reported a separate campaign involving extensive password spray attacks aimed at thousands of organizations, including several within the defense sector. Across 2023, APT33 showed interest in US and other country’s organizations in satellite, defense, and pharmaceuticals. The September attack was a culmination of probes across the year, resulting in data theft from a limited number of victims in these sectors.
This persistence underlines the group’s unwavering focus on acquiring military secrets and potentially disrupting critical infrastructure. APT33 has attacked sectors across the United States, Saudi Arabia, and South Korea over the past decade, with targets ranging from government, defense, and research, to finance and engineering.
Just two years ago, an Iran-linked hacking group known as DEV-0343 attacked US and Israeli defense technology companies. A stricter measure of cybersecurity control from businesses and those they rely on, chiefly Microsoft in this case, is necessary to ensure protection from foreign attacks and the loss of critical data.

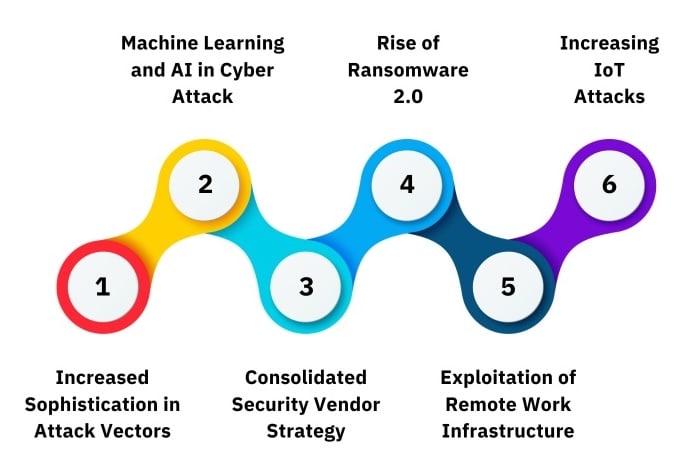
Top 6 Cybersecurity Threats in 2024
Unfortunately, defense contractors don’t exist in a vacuum. Cyber-espionage campaigns targeting this sector are merely one piece of a larger puzzle. In recent years, defense agencies and contractors worldwide have faced relentless attacks from:
- Russian state hackers: Espionage campaigns aimed at military intelligence and technological secrets.
- North Korean hacking groups: Attempts to steal confidential information and potentially disrupt critical infrastructure.
- Chinese cyber-espionage operations: Long-term efforts to acquire classified information and technological know-how.
This global landscape of cyber threats emphasizes the need for robust cybersecurity measures across the entire Defense Industrial Base.
In fact, this isn’t the first government-based security issue of 2023, with the CISA Citrix Sharefile Bug having occurred in September. That issue resulted in an uptick in suspicious activity, with many attempts to capitalize on the vulnerabilities caused by the bug. Many shady individuals are waiting to jump in and take as much as they can, or hide in your systems to wait out the storm and steal information when it’s safe. Unfortunately, government-related entities are considered a prime candidate for exploitation or manipulation on the cybersecurity front.
How to Protect Yourself from APT33 Hacker Group
Microsoft recommends several critical steps for defense contractors to defend against APT33 and other advanced hacking groups: TABLIZE THE FOLLOWING
- Reset credentials: Implement stringent password policies and immediately reset credentials for accounts targeted in spray attacks.
- Revoke session cookies: Minimize attack surface by invalidating any previously established session cookies.
- Secure accounts: Enforce multi-factor authentication (MFA) for all accounts, including those used for RDP and Windows Virtual Desktop.
- Stay vigilant: Implement ongoing security training and awareness programs to educate employees about phishing and other common cyber threats.
The ever-evolving landscape of cyber threats demands constant vigilance and proactive measures. By remaining informed, prioritizing robust cybersecurity practices, and collaborating with security experts, defense contractors can safeguard their vital technologies and information from groups like APT33.



